WASHINGTON (AP) — Exactly seven months before the 2016 presidential election, Russian government hackers made it onto a Democratic committee’s network.
One of their carefully crafted fraudulent emails had hit pay dirt, enticing an employee to click a link and enter her password.
That breach of the Democratic Congressional Campaign Committee was the first significant step in gaining access to the Democratic National Committee network.
To steal politically sensitive information, prosecutors say, the hackers exploited some of the United States’ own computer infrastructure against it, using servers they leased in Arizona and Illinois. The details were included in an indictment released Friday by special counsel Robert Mueller, who accused the GRU, Russia’s military intelligence agency, of taking part in a wide-ranging conspiracy to interfere in the 2016 presidential election. The companies operating the servers were not identified in the court papers.
The Russians are accused of exploiting their access to inexpensive, powerful servers worldwide — conveniently available for rental — that can be used to commit crimes with impunity. Reaching across oceans and into networks without borders can obfuscate their origins.
The indictment painstakingly reconstructs the hackers’ movements using web servers and a complex bitcoin financing operation.
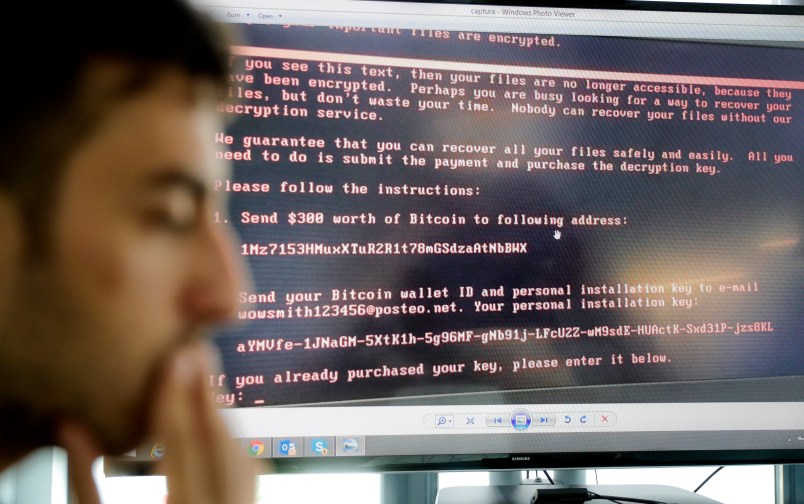
Two Russian hacking units were charged with tasks, including the creation and management of a hacking tool called “X-agent” that was implanted onto computers.
The software allowed them to monitor activity on computers by individuals, steal passwords and maintain access to hacked networks. It captured each keystroke on infected computers and took screenshots of activity displayed on computer screens, including an employee viewing the DCCC’s online banking information.
From April to June 2016, the hackers installed updated versions of their software on at least 10 Democratic computers. The software transmitted information from the infected computers to a GRU-leased server in Arizona, the indictment said. The hackers also created an overseas computer to act as a “middle server” to obscure the connection between the DCCC and the hackers’ Arizona-based server.
Once hackers gained access to the DCCC network, it searched one computer for terms that included “hillary,” ”cruz,” and “trump” and copied select folders, including “Benghazi Investigations.”
In emails, the hackers embedded a link that purported to be a spreadsheet of Clinton’s favorability ratings, but instead it directed the computers to send its data to a GRU-created website.
Meanwhile, around the same time, the hackers broke into 33 DNC computers and installed their software on their network. Captured keystrokes and screenshots from the DCCC and DNC computers, including an employee viewing the DCCC’s banking information, were sent back to the Arizona server.
The Russian hackers used other software they developed called X-Tunnel to move stolen documents through encrypted channels to another computer the GRU leased in Illinois.
Despite the use of U.S.-based servers, such vendors typically aren’t legally liable for criminal activities unless it can be proved in federal court that the operator was party to the criminal activity.
A 1996 federal statute protects internet vendors from being held liable for how customers use their service, and except for a few exceptions, provides immunity to the providers. The law is considered a key part of the legal infrastructure of the internet, preventing providers from being saddled with the behemoth task of monitoring activity on their servers.
“The fact that someone provided equipment and or connectivity that was used to engage in data theft is not going to be attributed to the vendor in that circumstance,” Eric Goldman, a professor of law and co-director of the High Tech Law Institute at Santa Clara University School of Law, said. A notable exception, however, is if federal prosecutors are bringing a criminal charge for violations of a federal criminal law.
In that case, “we’re going to require a high level of knowledge of their activity or intent,” Goldman said.
When the DNC and DCCC became aware they had been hacked, they hired a cybersecurity firm, Crowdstrike, to determine the extent of the intrusions.
Crowdstrike, referred to as “Company 1” in the indictment, took steps to kick the hackers off the networks around June 2016. But for months the Russians eluded their investigators and a version of the malware remained on the network through October — programed to communicate back to a GRU-registered internet address.
“We do not have any information to suggest that it successfully communicated,” said Adrienne Watson, the DNC’s deputy communications director.
As the company worked to kick them off, GRU officials allegedly searched online for information on Company 1 and what it had reported about its use of X-Agent malware and tried to delete their traces on the DCCC network by using commercial software known as CCleaner. Though Crowdstrike disabled X-agent on the DCCC network, the hackers spent seven hours unsuccessfully trying to connect to their malware and tried using previously stolen credentials to access the network on June 20, 2016.
The indictment also shows the reliance of Russian government hackers on American technology companies such as Twitter, to spread its stolen documents.
The hackers also accessed DNC data in September 2016 by breaking into DNC computers hosted on the Amazon Web Services’ cloud. The hackers used Amazon Web Services’ backup feature to create “snapshots” that they moved onto their own Amazon cloud accounts. Amazon also provides cloud computing services for various government agencies, including the Central Intelligence Agency.






I am a patient man, at my age. And I know that if I wait, patiently, long enough, I am going to eventually find out how the Alpha Bank server located inside Trump Tower during the Presidential Campaign, fits in with all of this.
And the amount of free software out there available to prevent stuff like this over the last ten years might’ve prevented this in the first place.
I had an IT manager once upon a time (in the 90’s, to be honest) who decided that NO one would get access to the internet because he didn’t want to be responsible for a hack. That was then. Apparently the DNC was no better just five years ago.
From the above, “Despite the use of U.S.-based servers, such vendors typically aren’t legally liable for criminal activities unless it can be proved in federal court that the operator was party to the criminal activity.”
I know this is a bit wonky, and perhaps a bit off topic, but the above comment illustrates exactly why the Internet and it’s infrastructure should be considered a “Public Utility”. Every law which governs the criminal and civil penalties are supported on the foundation of “Public Utility” jurisprudence. This is another clear difference between the Parties. The GOP has supported treating it a like an open marketplace, not a utility that all societies should be guaranteed and required such as roads, power, and water. The democrats believe that the internet should be treated the same.
Dana Milbank has a “smart” headline and a decent article on all this:
Weeeeeelll … sure, they obviously could have done better than they did. But, for a bit of perspective, cybersecurity is my Day Job, and it is a maxim that 100% prevention is basically impossible, and anyone promising such a thing is (a) either confused or dishonest, and (b) definitely selling something. The goal is to keep as much stuff as possible out, but also to understand that a sufficiently advanced, determined, persistent, and/or lucky adversary will eventually get in. At that point, the game becomes one of limiting the damage through a combination of segmenting your network and having decent monitoring and detection systems.
This is why a physical bank location has both a stout lock on the door and motion detectors on the inside.
Not excusing any lapses. Just want to point out that the mere fact that a breach occurred is not automatically evidence of incompetence.